A previously unknown threat actor called AeroBlade has been discovered by the BlackBerry Threat Research and Intelligence team [2]. This actor recently targeted a US aerospace company in a yearlong cyberespionage campaign. The attack utilized spear-phishing tactics as a delivery mechanism and is suspected to be part of a larger cyber espionage mission.
Description
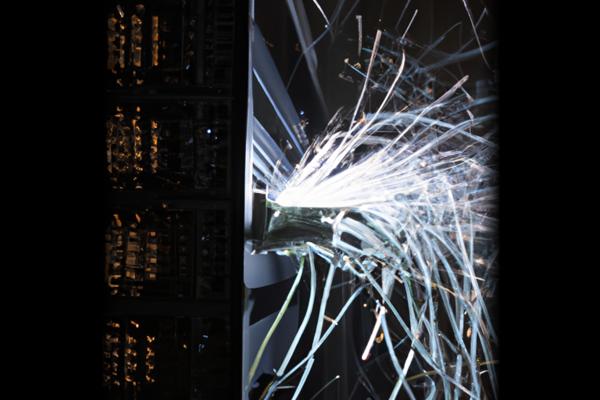
The origin of AeroBlade is currently unknown [3], and it is unclear if the attack was successful [3]. The attackers employed a weaponized document that contained a remote template injection technique and a malicious VBA macro code [1] [2]. This campaign went undetected for nearly a year due to anti-analysis protections [4]. The attack chain ultimately led to the deployment of a heavily obfuscated DLL that acted as a reverse shell, enabling the attackers to take control of the targeted device. The DLL incorporated anti-analysis and anti-disassembly techniques. The extent of the data accessed and the overall success of the campaign remain unknown. However, it is evident that the threat actor invested significant effort into developing additional resources to secure access to valuable information and successfully exfiltrate it. The AeroBlade campaign showcases the sophistication of cyber threats in the espionage domain [2], as the actor continuously adapts techniques and toolsets to avoid detection and enhance capabilities over time [2].
Conclusion
The AeroBlade campaign highlights the serious impact of cyber espionage on organizations, particularly those in sensitive industries such as aerospace. It underscores the need for robust cybersecurity measures to detect and prevent such attacks. As threat actors like AeroBlade continue to evolve and refine their tactics, organizations must remain vigilant and proactive in implementing effective mitigations. The implications of this campaign extend beyond the immediate incident, serving as a reminder of the ongoing and evolving nature of cyber threats in the espionage domain.
References
[1] https://thehackernews.com/2023/12/new-threat-actor-aeroblade-emerges-in.html
[2] https://cybermaterial.com/aeroblade-cyber-espionage-unveiled/
[3] https://cyber.vumetric.com/security-news/2023/12/05/new-threat-actor-aeroblade-emerges-in-espionage-attack-on-u-s-aerospace/
[4] https://www.darkreading.com/cyberattacks-data-breaches/aeroblade-cyberthreat-hacks-us-aerospace-company