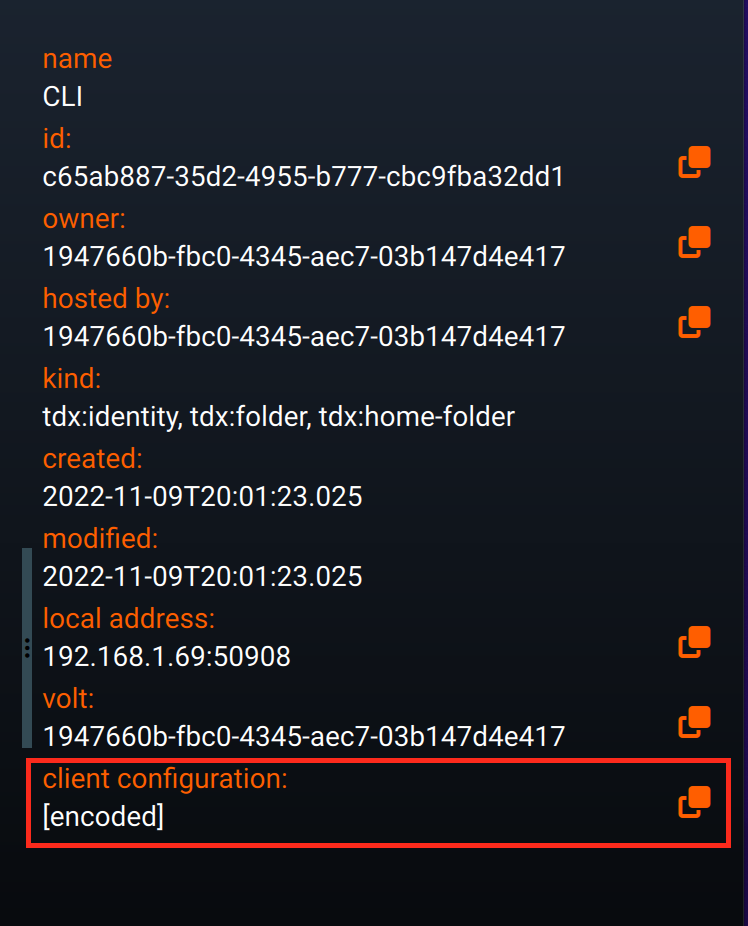
secure AI agents
Distributed Identity
Fully distributed identity suitable for cloud and peer to peer. Backed with strong crypto.
Service Management

Extensible Claims
Smart Policy
Tunnelling

Encryption
The security policy is attribute-based and borrows heavily from the XACML standard in terms of functionality. It provides an extremely versatile and extensible framework for controlling who can access what and when. For example it is possible to express rules such as ‘Nick can access my geolocation service and view my current location between 9am – 5pm Monday to Friday’.
| Client Authentication | Server Authentiation | Supported | Notes |
|---|---|---|---|
| certificate | certificate | yes | This is the default configuration in which mutual certificate authentication is used |
| certificate + token | certificate | yes | The client provides both a certificate and JWT. |
| token | certificate | yes | The client only presents a JWT with no client certificate. This is useful in scenarios where storing a private key is impractical |
| none | certificate | no | The client must always provide some authentication |
| certificate | none | no | The server must always present a certificate. |
| token | none | no | The server must always present a certificate. |
| none | none | no | Insecure |
| Kind | Description |
|---|---|
| tdx:cloud-connection | Represents a connection to a cloud-based tunnel. |
| tdx:database | A database. |
| tdx:group | A group of identities. |
| tdx:http-proxy | An HTTP forward proxy resource. |
| tdx:http-server | An HTTP server resource. |
| tdx:identity | An identity resource. |
| tdx:service | The top-level service kind. |
| tdx:sqlite-database | A sub-kind of Database, representing an Sqlite database. |
| tdx:sqlite-server | SqliteServer |
| tdx:symbolic-link | A file or folder that is linked directly to the local file system. |
| tdx:volt-link | Used by the fusebox to store links to other Volts |
| tdx:web-view | Used by the fusebox to display web pages. Experimental, macOS only. |
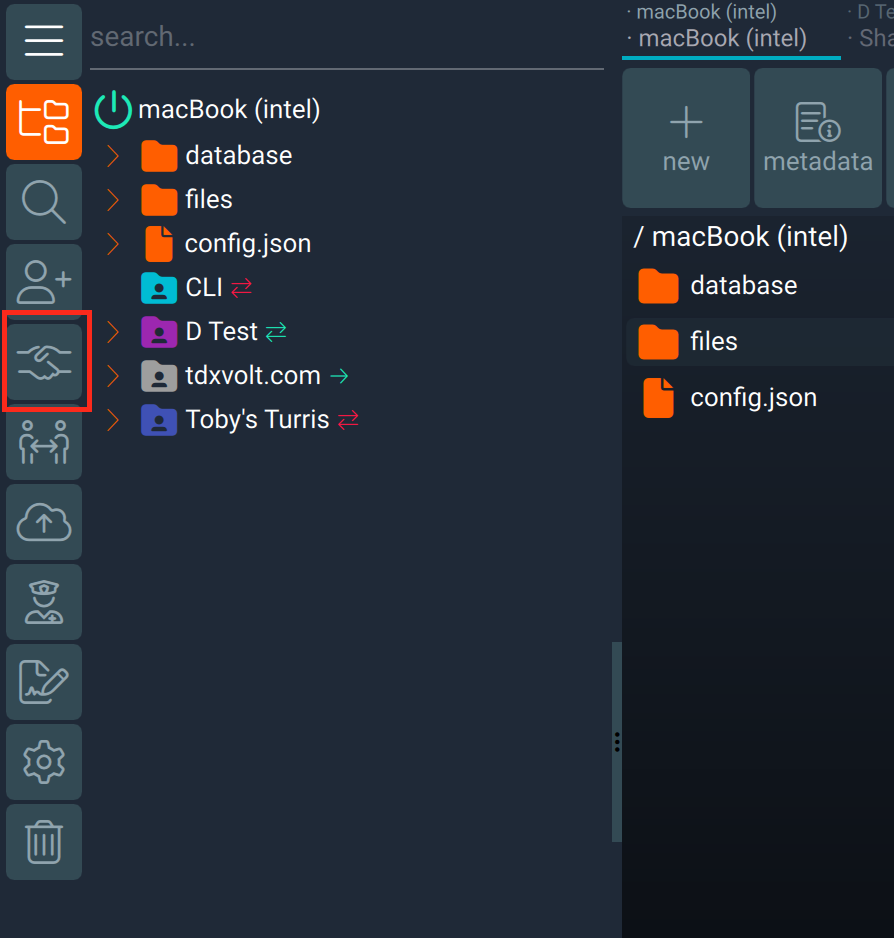
| tdx:wire | A wire resource. |
A resource is the fundamental entity in the tdx Volt. Various kinds of resource exist out of the box, including services, folders, files, and databases. Custom resource types are also supported. A simple, clean hierarchical taxonomy is used to classify resources. A single file or entire folder hierarchies can easily be uploaded or linked to the tdx Volt and made available from anywhere, given the correct authentication and authorisation as determined by the security policy. Databases can quickly be created and data ingested using a drag-and-drop interface. This too can then be made available for reading or writing anywhere using the appropriate security policy rules.